A step by step tutorial on how enable DNSSEC for your domain with the Knot DNS server version 2.8.0 released last week on 2019-03-05.
I am going to assume you:
- Have control over a second level domain like
estada.ch - Have a registrar that supports DNSSEC, see the last step to check this.
- Have a machine to run Knot on, can be a virtual machine (search for VPS and your country)
- Have the latest Debian 9 stable installed on that machine
- If you plan to run Knot remotely:
- OpenSSH configured on the server
- and the
openssh-clienton your machine
- Know how to become root (eg. with sudo)
- Have access to the Knot DNS Manual
For simplicity I use estada.ch as the example in the whole article.
Configure your machine as name server (Glue records)
Write an email or open a support ticket at your registrar to supply your machine as name server.
Request that they register your machine ns1.estada.ch with your addresses eg. 2a0a:51c0::61 and 185.194.239.73.
Note this manual process usually takes some time sometimes a business day.
Configure the public IPs
Debian Network Configuration on servers is usually done with /etc/network/interfaces.
For other distributions you best search the internet.
Install Knot
Add the source of the Knot software to by creating this file /etc/apt/sources.list.d/knot.list with that content:
deb https://deb.knot-dns.cz/knot-latest/ stretch main
Then save the certificate to the system:
curl https://deb.knot-dns.cz/knot-latest/apt.gpg > /etc/apt/trusted.gpg.d/knot-latest.gpg
And install the dependencies and the package:
apt install apt-transport-https
apt update && apt upgrade
apt install knot
Configure Knot to load the zone
Create the file /etc/knot/knot.conf with the following contents:
#
# This is a sample of a minimal configuration file for Knot DNS.
# For more details, see man 5 knot.conf or refer to the server documentation.
#
server:
# Listen on all configured IPv4 interfaces.
listen: 0.0.0.0@53
# Listen on all configured IPv6 interfaces.
listen: ::@53
# User for running the server.
user: knot:knot
rundir: "/run/knot"
mod-rrl:
- id: default
rate-limit: 200 # Allow 200 resp/s for each flow
slip: 2 # Every other response slips
log:
# Log info and more serious events to syslog.
- target: syslog
any: info
policy:
- id: rsa2k
algorithm: RSASHA256
ksk-size: 4096
zsk-size: 2048
nsec3: on
- id: ececc
algorithm: ecdsap384sha384
nsec3: on
template:
- id: default
storage: "/var/lib/knot"
dnssec-signing: on
dnssec-policy: rsa2k
global-module: mod-rrl/default # Enable RRL globally
zone:
# Master zone.
- domain: estada.ch
file: "/etc/knot/estada.ch.zone"
zone:
# Some other zone
- domain: somethingelse.ch
file: "/etc/knot/somethingelse.ch.zone"
The rate-limit is to prevent your DNS server from being misused in an DNS amplification attack.
Note your server is in the role of the primary resolver. That means most of your legitimate users will use their ISP's DNS as an intermediate and
Configure your zone
To configure DNS you must supply the DNS server Knot with a zone file. So for example the start of my zone currently looks like this:
estada.ch. 86400 SOA ns1.estada.ch. dnsadmin.estada.ch. 2019020203 14400 600 2419200 600
estada.ch. 86400 NS ns0.estada.ch.
estada.ch. 86400 NS ns1.estada.ch.
estada.ch. 86400 AAAA 2a0a:51c0::61
estada.ch. 86400 A 185.194.239.73
The SOA line describes the following fields:
- primary name server
- email of the zone administrator
- serial with the last updated date encoded plus a two digit counter, increase with every edit
- refresh every
14400seconds - retry every
600seconds - expire after
2419200seconds - minimum delay retry for
600seconds for negative results
Note that the Knot daemon will change this file and extend it with the hashes and NSEC3 records.
Get you DNSKEY id 257
After you reloaded the Knot service with this command:
sudo systemctl reload knot
You can get the public part of your zone file with this command:
sudo keymgr estada.ch dnskey
If you need the DS form of the key run run this command:
sudo keymgr estada.ch ds
Publish on your registrar
After logging in to the control panel of your registrar, search for the DNS configuration option of your domain.
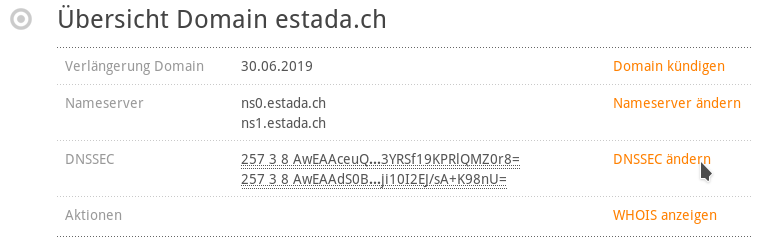
Then to enter your new KSK-Hash paste all currently valid entries in the form.
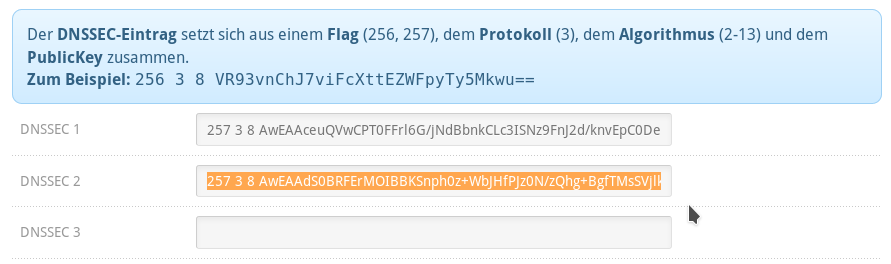
I use a special setup with two chains, so I have to enter two KSK hashes.
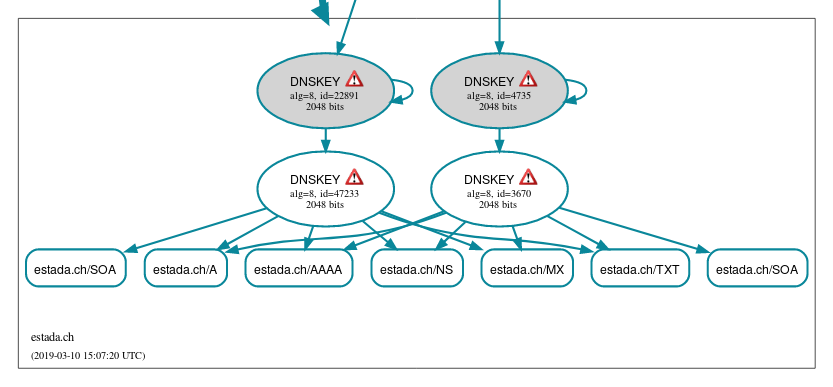
Test the publication with dnsviz.net
The tool dnsviz.net is a very popular graphical tool.
To check the configuration of estada.ch we can use this link:
http://dnsviz.net/d/estada.ch/dnssec/
If everything worked, you should see your chain terminate like the left part in this picture:
Test the publication by hand
Compare the output of the DS generated by the Knot DNS server with this command:
sudo keymgr estada.ch ds
Search for the last three parts of the output with the output of the kdig command from the knot-dnsutils or the dig command from the dnsutils package.
kdig ANY @a.nic.ch estada.ch +dnssec
Important if you are using the dig you must remove the space seperating the last 8 characters like this:
8 2 28521FE33926668A3D12B6212DA003226CAAD44430D6355F990BAAAD 8EAB2B3E
X Y >------------------------ remove space here ------------^
Notice that the server responsible for the .ch domains is a.nic.ch.
If your second level domain does not belong to .ch you need to lookup the primary primary server.
What if my registrar does not support DNSSEC?
First you should ask the support team of your provider. Maybe their interface is hidden or even via email.
Sadly some companies like metanet to this day do not support DNSSEC and your only option is to transfer the domain to another registrar like cyon or hosttech.
Switch just broke my setup with CDS (Child DS)
Switch has enabled the new feature CDS (Child DS). The goal was to simplify DNSSec provisioning, but it breaks existing setups with two independent ksk-chains.
You can test your domain with their new tool.
I need more help
Zeroth, test your setup with tools like dnsviz or MX Toolbox.
First, ask a friend or two. DNS is an old topic, so it has grown over time and sometimes the complexity is no longer obvious to people who did work those problems for a long time.
Second, read more documentation or reach out to strangers. If you ask nicely and lead with the work you already invested people tend to help you on the internet.
 Donate ♥
Donate ♥
 Imprint
Imprint
 Datenschutz
Datenschutz
 Archive
Archive




